Permission section
First 3 columns means user owner, second 3 columns means owner group, the third 3 columns means all others. And there is one letter D or – before these basically means the type of the object: directory or file.
Permission and File operation
Read permission:
- File: that user can use the cat, more, head, tail, less, ,and od commands to view its contents.
- Directory: user can use ls to view the files in it.
Execution permission:
- File: execute the file in memory.
- Directory: user can enter the directory and work with the directory content, such as issue cd command to change current working directory into it.
Also be referred to as the search permission or light switch. So, it is a quick way to deny a user from accessing a directory and all of its contents.
Write permission:
- Directory: allow user to add or remove file from the directory.
- File: Can open read edit the file, or delete the file.
Change owner or group
chown <new_owner> <files or directories>: change the ownership of the file or directory to the new user. you can add the -R to change group ownership recursively throughout the directory tree.
chgrp <new_owner_group> <files or directories> : change the owner group of the file or directory.
change both the owner and the group owner at the same time using chown command: chown <new_owner>.<new_file or directories>
Or you can use ” : ” instead of ” . ” but keep in mind that there should be no space before and after the column or dot.
Chmod command
It is used to change the permission for a certain file or directory. It takes two arguments, the first argument specifies the criteria used to change the permission, the second one is the object.
Two ways to change the permission:
1, Use letter:
chmod <category><operation><permission> <files or directories>
- Category: u (user), g (group), o (other), a (all categories)
- operation: + ( add a permission), -(remove a permission), = (makes a permission equal to)
- Permission: r (read), w (write), x (execute)
Example: chmod u+w, g+r-w, o+r-x file1
Note: You should ensure that there are no spaces between any criteria used in the chmod command, because all criteria makeup the first argument only.
if there is no character specifying the category of user to affect, all users are assumed,
2, Use numeric criteria:
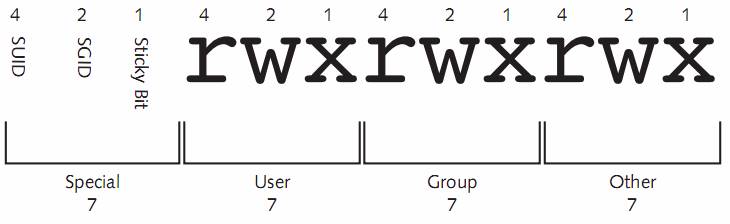
All permissions are stored in the inode of a file or directory as binary powers of two:
• read = 22= 4
• write = 21= 2
• execute = 20= 1
Thus, the mode of a file or directory can be represented using the numbers 421421421 instead of rwxrwxrwx. Because permissions are grouped into the categories user, group, and other,you can then simplify this further by using only three numbers, one for each category that represents the sum of the permissions.
To change the mode of the file1 file used earlier to r-xr—–, you can use the command chmod 540 file1
Default permission and Umask
Default permission for a file: rw-rw-rw-
Default permission for a directory: rwxrwxrwx
umask( user mask): used to takes away permissions on newly created files and directories. Most common one is 022.
Note that: umask applies only to newly created files and directories;it is never used to modify the permissions of existing files and directories. You must use the chmod command to modify existing permissions.
 To set the umask:
To set the umask: umask <numeric_permission_expression>
To verify the umask: umask
Special permissions
SUID:
Set on a file, the person who executed the file temporarily becomes the owner of the file while it is executing. Such as /usr/bin/passwd.
SUID can only be applied to binary compiled programs. The Linux kernel does not let you apply the SUID to a shell script.
SGID:
Apply both to files and directories. SGID allows regular users to execute a binary compiled program and become a member of the group that is attached to the file.
If a command or file requires the user executing it to have the same permissions applied to the sys group, setting the SGID on the files implifies assigning rights to the file for user execution.
Special function:
when placed on a directory. When a user creates a file, recall that that user’s name and primary group become the owner and group owner of the file,respectively.
However,if a user creates a file in a directory that has the SGID permission set (note that if the user create a file in a directory, he is executing folder, so he become a member of the group that attached to the folder), that user’s name becomes the owner of the file and the directory’s group becomes the group owner of the file.
Sticky bit:
Used to lock the files in memory,
Today only used on directory, so user can add files to the directory but only delete those files that they have added and not others.
Set the special permission
1, Because special permissions require execute, they mask the execute permission when displayed using the command. As show bellow in mode:
2, The system allows you to set special permissions even if the file or directory does not have execute permission.However,the special permissions will not perform their function.
If the special permissions are set on a file or directory without execute permissions,then the ineffective special permissions are capitalized. As shown:
3, Set special permission in numeric:
chmod 6755 file1
the first bit 6 means the special permission SUID and SGID.
If you issue ls -l command, the file1 line should be -rwsr-sr-x .
if you issue chmod 7665 file1 , then issue ls -l command, the file1 line should be -rwSrwSr-t .
Setting permission in the ACL
Set the extra acl to the file or directory, the permission is finely grained.
Command: setfacl <option> <category>:<user_or_group_name>:permission <filename_or_directory>
Option:
The -m (--modify) and -M (--modify-file) options modify the ACL of a
file or directory. ACL entries for this operation must include permissions.
The -x (--remove) and -X (--remove-file) options remove ACL enries.
Only ACL entries without the perms field are accepted as parameters,
unless POSIXLY_CORRECT is defined.
When reading from files using the -M, and -X options, setfacl accepts
the output getfacl produces. There is at most one ACL entry per line.
After a Pound sign (‘#’), everything up to the end of the line is
treated as a comment.
-b, --remove-all
Remove all extended ACL entries. The base ACL entries of the owner,
group and others are retained.
-k, --remove-default
Remove the Default ACL. If no Default ACL exists, no warnings are
issued.
-n, --no-mask
Do not recalculate the effective rights mask. The default behavior
of setfacl is to recalculate the ACL mask entry, unless a mask
entry was explicitly given. The mask entry is set to the union of
all permissions of the owning group, and all named user and group
entries. (These are exactly the entries affected by the mask
entry).
--mask
Do recalculate the effective rights mask, even if an ACL mask entry
was explicitly given. (See the -n option.)
-d, --default
All operations apply to the Default ACL. Regular ACL entries in the
input set are promoted to Default ACL entries. Default ACL entries
in the input set are discarded. (A warning is issued if that hap-
pens).
Verify: use ls -l to verify, you can see a + symbol next to the mode to indicate that there are additional entries.
To check the additional members, use getfacl command.
If the mask is more restrictive,it takes precedence when it comes to permissions. The mask is always made equal to the least restrictive permission assigned.
To remove all extra ACL assignments on the doc1 file,simply use the –b option.
Managing filesystem attributes
To see the file system attributes that are currently assigned to a file,you can use the lsattr (list attributes)command.
By default, all files have the e attribute, which write to the file in “extent” blocks(rather than immediately in a byte-by-byte fashion). If you would like to add or remove attributes, you can use the chattr (change attributes)command.
use + or – t add or remove attribute.
i attribute: immutable attribute, not even the root user can modify a file that has the immutable attribute set.